Application Model Auth Complete Rocket Casino Login Australia

Usage Model Verification is becoming increasingly important in online gaming, https://rocketcasinoo.com/login/, particularly in Australia. Full Rocket Casino Sign-In incorporates this technique to improve user security. By analyzing distinct behaviors, such as keystroke speed and navigation patterns, it creates a adaptive environment for identity verification. This raises inquiries about its efficacy and user experience. What underlying systems back this adaptive approach, and how do players perform with this advanced security layer in practice?
Understanding Application Pattern Authentication
While conventional authentication techniques often rely on static usernames and passwords, usage pattern authentication provides a adaptive method to confirming identity. This technique involves analyzing user behavior to create a unique profile that mirrors how an individual typically engages with a system.
Factors such as keystroke speed, navigation patterns, and device usage add to a behavior fingerprint. When a user tries to log in, this fingerprint is matched to the saved profile, allowing for real-time verification. If patterns deviate significantly, extra verification steps may be initiated.
This innovative security approach improves protection against unauthorized access while offering a smoother user experience. Therefore, application model authentication represents a progressive shift in how identity verification is handled in the digital environment.
Advantages of Full Rocket Casino Sign-In
What advantages does a complete Rocket Casino sign-in provide to users?
A complete login improves security, ensuring that personal and financial information remains protected from unauthorized access. This system promotes a efficient user experience, allowing for fast access to gaming features and account management options.
Furthermore, users can benefit from personalized content and promotions designed to their preferences, enhancing overall engagement. The login procedure also facilitates easy monitoring of gameplay history and rewards, permitting better judgment in gaming activities.
Additionally, it aids in the use of responsible gaming practices, as users can set limits and observe their activity more efficiently.
How Usage Pattern Auth Works
Usage Pattern Authentication (Auth) improves security protocols by examining user conduct and interaction patterns within the system.
By monitoring various metrics, such as regularity of logins, time allocated on specific areas, and transaction histories, the system establishes a standard of normal operation for each user.
When variations from these established patterns happen, the system can mark them for additional scrutiny. For example, if a user suddenly logs in from a new machine or geographic area, the Auth may request additional verification steps.
This anticipatory strategy restricts unauthorized use and boosts user trust in the platform.
Consequently, Usage Pattern Auth serves as an adaptive security layer that changes based on individual user interactions, ensuring a more protected situation for all.
Security Features Enhancing Player Safety
Security aspects at Rocket Casino, such as two-factor authentication and data encryption techniques, play an essential role in securing player data.
Two-factor authentication provides an extra level of security by bloomberg.com demanding a second form of confirmation during login.
Meanwhile, data encryption protocols secure sensitive data, guaranteeing that player transactions are safe and private.
Two-Factor Authentication Benefits
As online gaming continues to grow in appeal, introducing two-factor authentication data-api.marketindex.com.au (2FA) has appeared as an significant action for improving player protection.
This safety measure adds an extra layer of protection by requiring users to verify their identity through a second method, typically a mobile device. By doing so, 2FA greatly reduces the risk of unauthorized access, shielding players from potential account takeovers.
Additionally, it fosters greater trust in online platforms, comforting players that their personal and financial information is safeguarded. Many gamers appreciate the peace of mind that comes with knowing their accounts are protected by more than just a password.
Ultimately, 2FA is a essential component of a comprehensive security strategy in online gaming.
Data Encryption Protocols
In the domain of online gaming, utilizing robust data encryption protocols is paramount for safeguarding player information.
These protocols employ sophisticated algorithms to protect sensitive data, ensuring that transactions and personal details remain confidential. Gamers can rest assured that their financial information is securely transmitted, reducing the risk of cyberattacks and data breaches.
Leading online casinos, like Rocket Casino, adopt protocols such as SSL (Secure Socket Layer) encryption, which encrypts data exchanged between players and the casino’s servers.
This level of security not only fortifies trust between players and the platform but also complies with industry regulations that mandate data protection standards.
Consequently, players are more likely to engage freely, knowing their information is protected from unauthorized access.
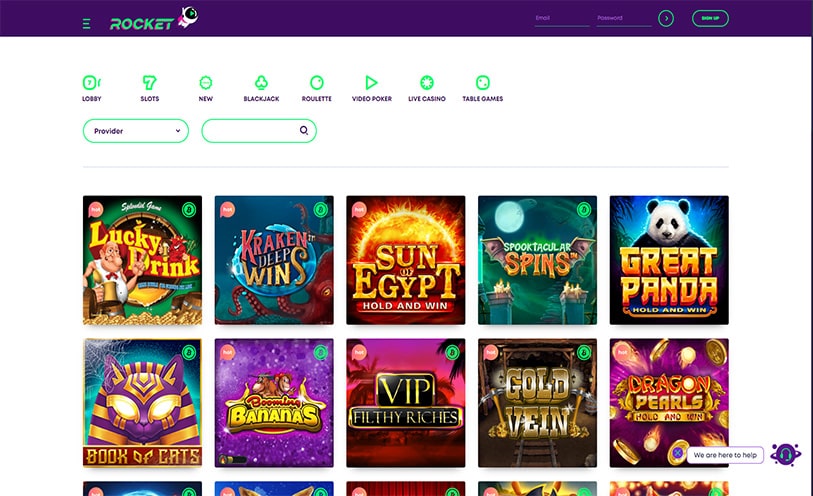
Step-by-Step Guide to Setting Up Your Login
Setting up a login for Rocket Casino in Australia involves a straightforward process that users can easily navigate.
First, users should navigate to the Rocket Casino site, where they will find the “Sign Up” button clearly visible. After selecting this button, they will be required to fill out a registration form, which requires essential personal information, including full name, email address, and date of birth.
Once the form is submitted, users must create a strong password, complying with the required guidelines. After completing the registration, users will receive a confirmation email to confirm their account.
Following this, they can log in using their registered email and password, finalizing the initial setup for accessing Rocket Casino’s features effectively.
Compatibility With Popular Gaming Devices
Rocket Casino prioritizes compatibility across various gaming devices, ensuring that players can enjoy a uninterrupted experience.
Both mobile devices and desktop setups are enhanced, providing users with adaptability and convenience.
This versatility allows gamers to engage with their favorite titles, regardless of their preferred platform.
Mobile Device Compatibility
While many online casinos strive for cross-platform functionality, Rocket Casino leads in mobile device compatibility, providing a uninterrupted gaming experience across multiple popular devices.
The platform has been optimized for both iOS and Android systems, allowing players to enjoy their favorite games on smartphones and tablets without interruption. It supports a variety of screen sizes and resolutions, scaling effortlessly to provide ideal visuals and performance.
Additionally, the mobile interface is easy to use, featuring simple navigation that boosts gameplay. Players can access a extensive selection of games, promotions, and banking options on the go, making it simple for gaming enthusiasts.
Desktop Gaming Experience
Players often find that the desktop gaming experience at Rocket Casino offers exceptional compatibility with a variety of popular gaming devices. This effortless integration enhances user satisfaction, making it effortless to immerse oneself in gaming activities.
The following devices are particularly acknowledged for their compatibility:
- Windows PCs – Configured for high performance and graphic fidelity.
- Mac Computers – Conveniently accessible, offering smooth gameplay and interface.
- Gaming Laptops – Provide portability without forfeiting performance.
- Tablets – Compatible with desktop features while ensuring versatility.
User Feedback and Experiences in Australia
User feedback regarding the login experience at Australian online casinos emphasizes a variety of perspectives, indicating both satisfaction and frustration.
Many users enjoy the uncomplicated process, noting that the efficient interface allows them to access their accounts quickly.
However, some players express irritation over intermittent glitches and slow loading times, which can interrupt their gaming flow.
Additionally, concerns regarding the security of personal information during the login process have been brought up, leading some users to feel apprehensive.
On the other hand, positive comments frequently mention quick customer support response when login issues occur.
Future Developments in Online Casino Authentication
How will progress in technology shape the future of online casino authentication? The progression of online security measures is vital for maintaining player trust and integrity in gaming platforms.
Key future developments in online casino authentication may include:
- Biometric Authentication
These advancements promise to enhance user experience while providing robust protection against unauthorized access and fraud.
Frequently Asked Questions
Can I Use Usage Pattern Auth on Multiple Devices?
Usage pattern authentication can generally be used on multiple devices, depending on the specific setup and service.
Some systems allow users to register multiple devices, facilitating a seamless experience across platforms.
However, limitations may exist based on security protocols and user settings.
It is advisable for users to review the terms and conditions of the service provider to understand the extent of multi-device support regarding usage pattern authentication efficiently.
Is There a Cost Associated With Using Usage Pattern Auth?
There is generally no direct cost associated with using usage pattern authentication. Most platforms implement this security feature as part of their overall service without charging users separately.
However, it is important for users to be aware of potential indirect costs, such as data usage if relying on mobile networks, or fees linked to device upgrades that may enhance security.
Consequently, careful consideration of the broader implications is advisable.
Can I Reset My Login Details Easily?
Indeed, resetting login details can usually be done easily. Most services supply a simple procedure for people to retrieve or change their login information or account details.
This usually entails selecting a “Forgot Password?” option, entering their registered email, and complying with the next steps provided via e-mail.
The whole process is designed to be user-friendly, making sure that users can recover access to their accounts without any excessive difficulty or wait.
What Happens if I Forget My Usage Pattern?
If an user loses their usage pattern, they generally lose admittance to their user account and may have to go through a retrieval procedure.
This frequently entails responding to security questions, authenticating who they are through email or mobile, or utilizing secondary recovery options.
It is important to check the service’s help resources for specific instructions to recover admittance.
People are advised to safely note their usage patterns or establish backup restoration methods to prevent future problems.
Is Usage Pattern Auth Available for International Players?
Usage pattern authentication is usually intended for particular areas, and its availability for international gamers can be subject to the system’s guidelines.
While certain online gaming platforms may offer this option to individuals worldwide, others might limit it based on region.
It is crucial for users to examine the terms and conditions of the system they are utilizing to ascertain they can access this verification method from their respective locations.
